YunoHost, super Energiesparend
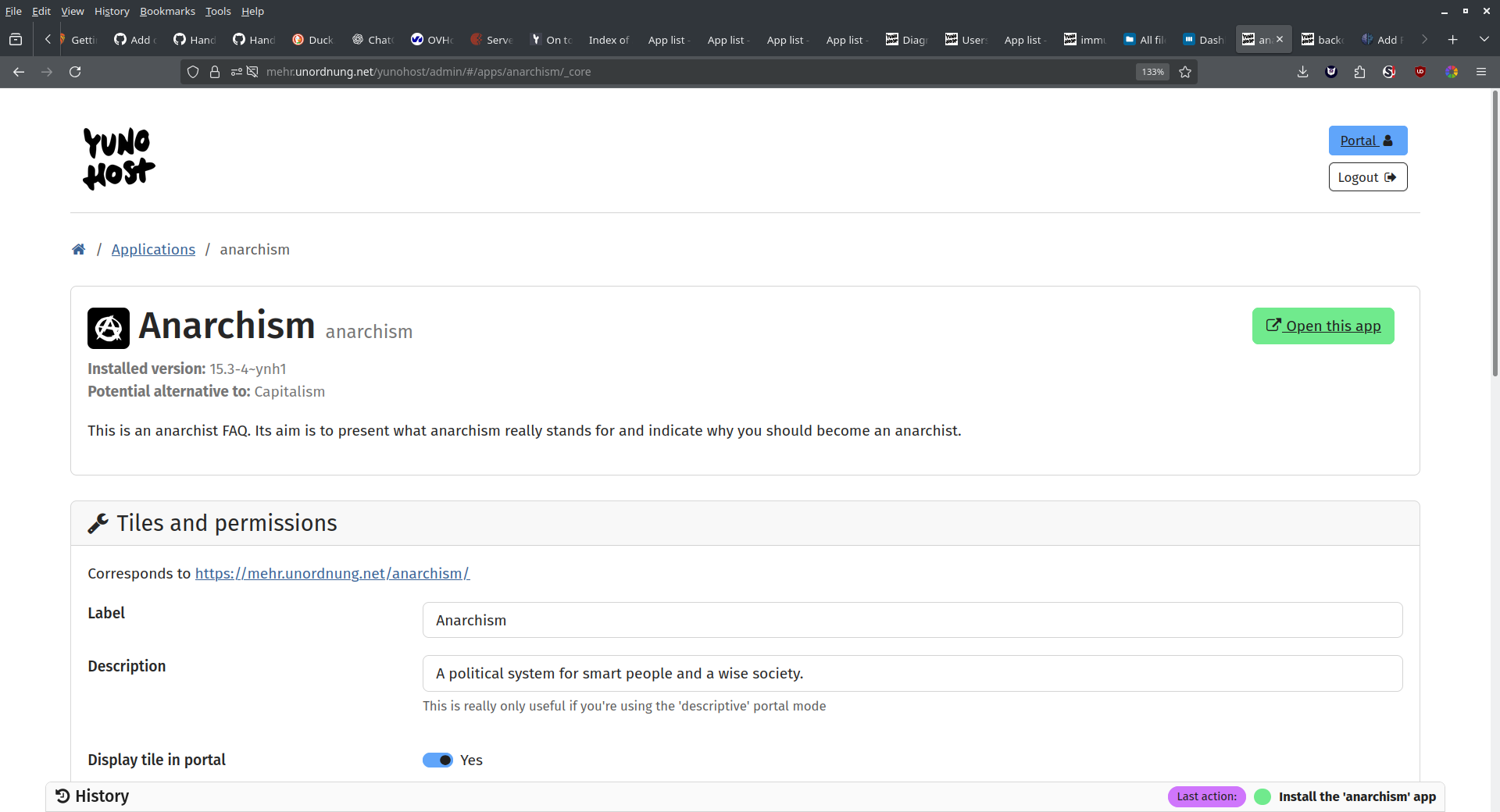
Install anarchism by one click 🙂 and not just that…all the useful apps and even custom apps it installs for you. Much love to YunoHost <3 While installing it on top on debian 12, i had some trouble with fail2ban. But then pure bliss. Running WordPress, Backdrop and Nextcloud with it, besides anarchism 😉 Well, … Read moreYunoHost, super Energiesparend